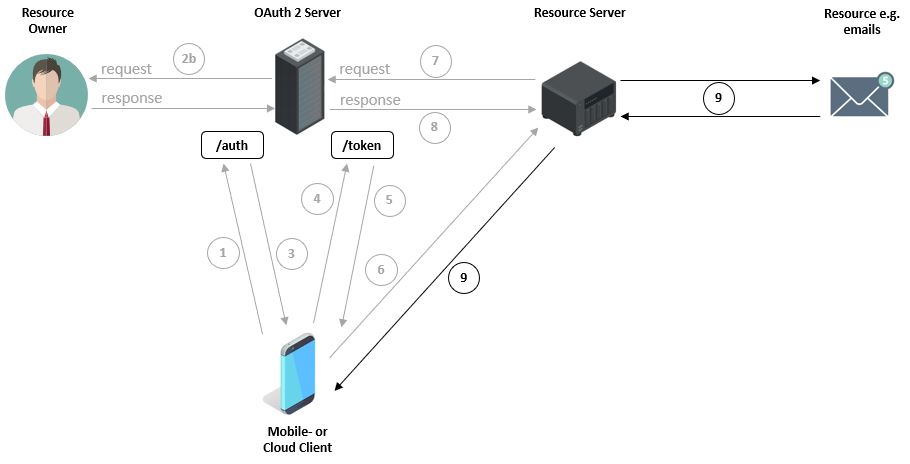
OAuth 2.0 Process (high level)
The first image shows how a user, with their device via a mobile application, e.g. an email program from an unknown company, wants to query emails (Resources) from, for example, a Google Server (Resource Server). For this purpose, the user must enter their Google credentials within the mobile application. However, this is associated with certain risks, since a) the email program can store the password and b) the application can use the password to, for example, access other Google services. ...