CoAP: Specification Summary (high level)
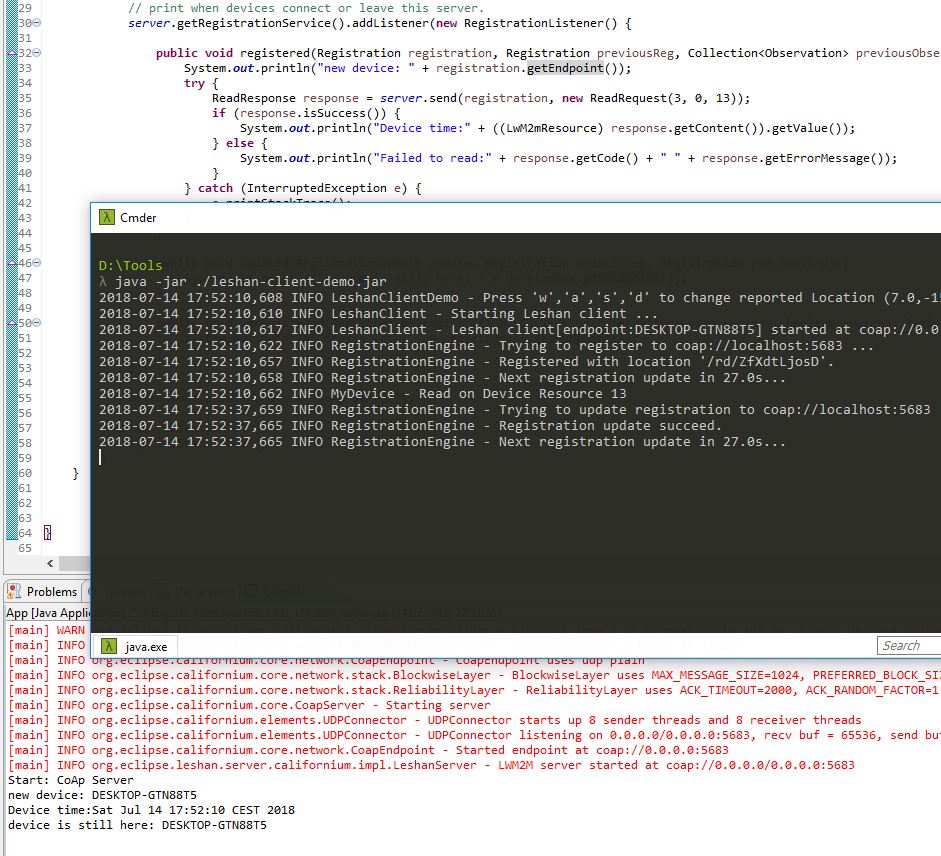
Constrained Application Protocol (CoAP) CoAP is an Internet application protocol specified in RFC 7252. The protocol is used for communication of devices ’nodes’, e.g. embedded devices, that consume very little energy (low-power) and operate in networks with increased data loss (lossy networks), for instance IPv6 over Low-Power Wireless Personal Area Networks (6LoWPANs). CoAP can also be used within Internet-based networks for mobile communication via SMS. CoAP is primarily used in the context of the Internet of Things (IoT) and Machine-to-Machine (M2M), as device data/sensor data of small size is usually transmitted. Since this type of data is transmitted at regular intervals (cycles), individual (lost) data packets have no significant impact on the processing systems or applications, such as an IoT platform that processes and/or graphically displays the corresponding sensor data (temperature, rotation speed, etc.). ...